What Is a Network Security Threat and Why It Matters
Discover what a network security threat is, why it’s crucial for businesses, and learn practical steps to protect your data and systems before it’s too late.

What if you were not aware that someone had taken control of your smart devices, read your private messages, or hacked into your bank account? Networks are necessary for almost everything we do these days, including banking, online shopping, talking, and utilizing smart devices. We run a greater risk of network security threats—attacks that can steal, corrupt, or block our data—the more we depend on them.
Not just IT workers should be aware of these dangers; anybody who works with technology should understand why network security is important and how to avoid it.
Network Security vs. Cybersecurity
Network security focuses on protecting an organization's internal network infrastructure. Its goal is to ensure that data and communications within the network are secure and reliable by defending servers, computers, and other devices from unauthorized access, attacks, or issues.
Key tools used in network security include firewalls, intrusion detection systems, and antivirus software. The main objectives are to prevent breaches, monitor traffic for unusual activity, and ensure that business networks operate smoothly. By achieving these goals, organizations can avoid costly losses and downtime caused by cyberattacks.
Cybersecurity is a comprehensive term that guards against online threats to all digital assets, including networks, apps, devices, and data. It seeks to protect an organization's complete digital ecosystem from ransomware, malware, phishing, hacking, and other online threats.
To stop data breaches, it also entails risk management techniques, training, and policies. In a world going more digital, cybersecurity protects an organization's reputation, financial stability, and credibility by guaranteeing not only technological safety but also regulatory compliance.
What Is a Network Security Threat?
Any potential threat that could take advantage of a network's weaknesses to steal, harm, or interfere with data and services is considered a network security threat. It's critical to differentiate between attacks, vulnerabilities, and threats:
-
A vulnerability is a weakness in your system.
-
A threat is the potential for harm.
-
An attack is the action that exploits the vulnerability.
For example, a weak password (vulnerability) can be exploited by hackers (threat) to gain unauthorized access (attack). Real‑life headlines of ransomware or data breaches show that threats are not just theoretical—they can have serious consequences. In fact, according to the India Cyber Threat Report 2026, India recorded over 265 million cyberattacks in 2025, with malware, ransomware and network exploits detected every minute across businesses and devices—highlighting just how common and dangerous these threats have become.
Why Network Security Matters in Today’s Digital World
Network security is essential in today's digital world since threats are increasing and any breach can damage confidence, finances, and businesses.
-
Growing Digital Reach: As networks grow due to remote employment, cloud services, mobile devices, and the Internet of Things, hackers have additional ways to attack sensitive data.
-
Compliance Demands: Strong network security is required by laws like the CCPA and GDPR, and breaking them can result in hefty fines.
-
Financial Risks: Attacks like ransomware cost billions of money-making cybercrime extremely profitable and motivating criminals to continue creating new techniques.
-
Business Continuity: Even brief outages can result in large financial and productivity losses, and network disruptions can halt regular operations.
-
Protecting Reputation: Customers' and partners' trust is damaged by security breaches, which makes it more difficult for companies to expand and stay credible.
Common Types of Network Security Threats
Network Security Threats come in many forms. Here are some of the most common:
1. Malware
Malware is software intended to harm, steal, or interfere with systems. It causes major network issues and spreads via downloads, emails, and compromised files.
Why It Matters: Every firm needs network protection since malware can cause financial loss, compromise critical data, and shut down operations.
2. Phishing & Social Engineering
Phishing is the practice of tricking someone into divulging financial information or passwords through phone calls, emails, or phony websites. Social engineering circumvents security mechanisms by manipulating human behavior.
Why It Matters: Being a victim can reveal personal information, damage one's reputation, and necessitate expensive rehabilitation, underscoring the importance of cautious network security and employee understanding.
3. Distributed Denial of Service (DDoS) Attacks
DDoS assaults cause traffic overload on systems, which prevents services from operating. Hackers target networks or websites, creating downtime and operational disruptions.
Why It Matters: Revenue and productivity are impacted by service outages. For corporate trust and operational continuity, DDoS attack defense is essential.
4. Man-in-the-Middle (MitM) Attacks
MitM attacks use user-system communication interceptions to insert malicious information or steal data. Unsecured networks and public Wi-Fi are frequent targets.
Why It Matters: Because sensitive information can be stolen undetected, encryption, secure connections, and careful network traffic monitoring are essential.
5. SQL Injection
SQL injection attacks take advantage of flaws in online applications to provide hackers access to databases and the ability to alter or steal private data.
Why It Matters: Customers and companies may experience data breaches. These hazards are successfully decreased by putting firewalls and safe coding techniques into place.
6. Insider Threats
Insider threats occur when contractors or employees misuse their access, whether on purpose or by accident, to compromise systems, steal information, or interfere with business operations.
Why It Matters: Monitoring, access controls, and stringent security measures are necessary because internal breaches can be more destructive than external attacks.
7. Zero-Day Exploits
Zero-day exploits target undiscovered vulnerabilities before they are fixed. Hackers move swiftly, taking advantage of these vulnerabilities to cause the most harm possible before being discovered.
Why It Matters: Systems and data are at immediate risk, so staying ahead of the curve requires proactive updates, security research, and threat information.
8. Credential Stuffing/Account Takeover
Attackers get access to accounts by using credentials that have been stolen, frequently from earlier data thefts. Automated tools boost the scale and pace of attacks.
Why It Matters: Financial and reputational harm can result from unauthorized access. It is essential to comprehend the significance of cybersecurity in order to avoid account hacks.
Businesses and individuals can identify possible risks early and take action to successfully secure their data and networks by being aware of these kinds of threats.
How Network Security Threats Work
Most attacks follow a common lifecycle:
-
Reconnaissance: Before starting an attack, attackers research users, systems, and networks to identify vulnerabilities.
-
Exploitation: They exploit weaknesses and obtain illegal access by using phishing, malware, and other techniques.
-
Propagation: After entering, the danger propagates via networks, devices, or systems in order to access private information and cause the most harm.
-
Impact: Financial, operational, and reputational harm can result from data theft, system disruptions, or service blocking.
-
Covering Tracks: To avoid detection and extend their stay, attackers may destroy evidence, turn off logs, or alter systems.
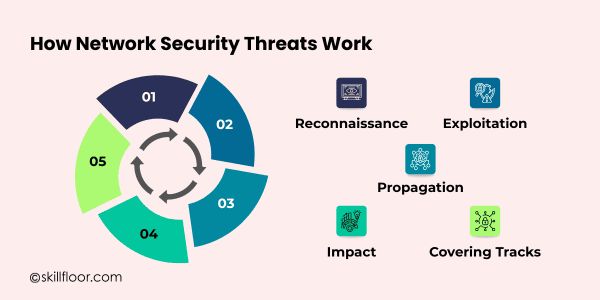
The need for proactive monitoring and multi-layered defenses, such as strong network security, in successfully safeguarding systems, data, and overall digital operations is made clearer by visualizing this process.
Why Network Security Threats Matter
The consequences of network threats are significant:
-
Financial Loss: Long-term financial stability and business profitability might be significantly impacted by ransom payments, outages, or fines associated with breaches.
-
Reputation Damage: Customers' trust may be damaged permanently by data breaches or service failures.
-
Legal and Compliance Issues: Penalties for breaking laws like GDPR, HIPAA, or PCI DSS can be severe.
-
Operational Disruption: Inefficient processes and commercial operations are caused by compromised systems, which also reduce productivity and stop services.
-
Intellectual Property Theft: Theft of confidential company information, trade secrets, or research can drastically diminish competitive advantage.
Underestimating or ignoring the increasing risks of network security threats can result in significant financial, operational, or reputational losses for both small enterprises and individual users.
Signs Your Network May Be at Risk
Being aware of potential warning signs can help you act early:
-
Unusual spikes in network traffic
-
Slower-than-normal system performance or frequent crashes
-
Unexpected login attempts or unauthorized access
-
Signs of data leaks or suspicious file changes
-
Unexplained software or configuration changes
Early detection of these warning indicators helps people and organizations react swiftly, stop additional harm, and successfully defend networks, systems, and sensitive data from growing security risks.
Effective Ways to Mitigate Network Security Threats Proactively
Staying ahead of attackers demands proactive network protection techniques. Risks can be decreased before significant harm is done by early prevention and ongoing monitoring.
-
Use Firewalls and Antivirus Software: Networks and devices are safeguarded by properly configured technologies, which aid in the efficient detection and defense against malware and illegal access.
-
Keep Systems and Software Updated: Frequent patches and upgrades minimize security threats by reducing vulnerabilities and stopping criminals from taking advantage of them.
-
Implement Strong Passwords and Multi-Factor Authentication: Adding extra authentication layers to complicated passwords helps protect accounts from unwanted access.
-
Train Employees on Security Awareness: Staff members' knowledge of phishing, scams, and internet safety improves defenses and lowers errors.
-
Monitor Networks and Backup Data: Regular backups protect data from changing cybersecurity threats, while ongoing monitoring spots anomalous activity early.
The Role of Emerging Technologies
New technologies are helping organizations stay ahead of threats:
-
AI and Machine Learning: Recognize odd trends, spot suspicious activity, and foresee possible attacks before they do any harm.
-
Zero Trust Security: Assumes that no user or device is inherently reliable and constantly checks access to reduce risks.
-
Cloud Security Solutions: Protect data handled and stored online while tackling the particular difficulties presented by remote access and cloud environments.
-
Quantum Computing Threats: Sensitive network data needs to be secured using sophisticated techniques because emerging quantum technologies have the potential to crack conventional encryption.
-
Automation and Orchestration Tools: Simplify threat identification and response to minimize human error and enable quicker action against assaults.
Case Studies / Real-World Examples
Target (2013): Over 40 million consumers' credit card information and personal information were stolen by hackers using shoddy network protections.
SolarWinds (2020): A supply chain hack exposed vital systems and impacted thousands of firms globally, including US government agencies.
Colonial Pipeline (2021): The East Coast's fuel supply was disrupted when a major US petroleum pipeline was forced to shut down due to a ransomware attack.
Equifax (2017): Due to unpatched software vulnerabilities, 147 million people's personal information was compromised, causing significant financial and reputational harm.
Maersk (2017): The shipping giant suffered damages estimated at $300 million and worldwide operational interruptions as a result of the NotPetya malware attack.
Frequently Asked Questions About Network Security Threats
Q1: Can network security threats affect personal devices?
A: Yes. Threats like malware, phishing, and ransomware can target personal computers, smartphones, and smart home devices.
Q2: Are free public Wi-Fi networks safe?
A: Public Wi-Fi is often unsecured, making it easier for hackers to intercept your data. Use a VPN for protection.
Q3: How quickly can a network threat cause damage?
A: Some attacks, like ransomware or malware, can damage systems and steal data within minutes if not detected early.
Q4: Do small businesses need network security measures?
A: Yes. Small businesses are often targeted due to weaker defenses, making them vulnerable to financial loss and data breaches.
Q5: Is antivirus software enough to prevent all threats?
A: No. Antivirus helps, but combining updates, firewalls, monitoring, and user awareness is essential for complete protection.
Technology alone won't keep you secure online; awareness and readiness are essential. Anyone can be affected by network security threats, from individuals using smart devices to large companies managing sensitive data. You can reduce risks and protect your information by understanding the various types of threats, being alert to warning signs, and taking simple precautions like updating software, using strong passwords, and monitoring your network. While new tools and technologies make it easier to stay ahead, developing good habits and staying attentive are just as important. A little planning today can help you avoid significant problems tomorrow.





























![A Complete Guide to 10 Cybersecurity Domains [2026 Update]](https://s3.us-east-1.amazonaws.com/skillfloor-website/uploads/images/202603/image_870x580_69ba9f637fe64.jpg)