A Complete Guide to 10 Cybersecurity Domains [2026 Update]
Master the 10 cybersecurity domains in 2026 and safeguard your career, company, and world. This guide equips professionals with essential skills and knowledge.
![A Complete Guide to 10 Cybersecurity Domains [2026 Update]](https://s3.us-east-1.amazonaws.com/skillfloor-website/uploads/images/202603/image_870x580_69ba9f637fe64.jpg)
Each year, millions of companies’ face cyberattacks that threaten their data and reputation. Imagine waking up to a news alert announcing that your company’s confidential data has been stolen. Panic ensues as crucial issues arise when client records, financial documents, and important projects vanish in an instant.
Currently, cyberattacks impact the entire company rather than just IT. They can risk careers, damage reputations, and destroy consumer confidence. Every professional, including developers and managers, must be aware of the dangers. These days, being ready is crucial for safeguarding your business and your own future.
What's good? Cybersecurity doesn't have to be intimidating or difficult. You can secure your data, lower risks, and boost your trust in your work by studying the 10 primary cybersecurity domains. You will be able to keep safe and prepared for anything with the help of this guide.
What are Cyber Security Domains?
The primary areas that group all the skills, information, and procedures required to safeguard computers, networks, and data are known as cybersecurity domains. They serve as a kind of road map, assisting professionals in identifying hazards and safeguarding data in a rapidly evolving digital environment.
Every domain concentrates on particular methods, resources, and techniques. Acquiring knowledge of all of these provides a comprehensive understanding of cybersecurity, assisting firms in averting threats, reacting promptly, and maintaining compliance. Professionals who comprehend these domains will feel more confident, advance in their careers, and be more equipped to deal with contemporary cyber threats.
Why Understanding Cybersecurity Domains Matters Now
Understanding cybersecurity domains is crucial in today's digital world to safeguard data, networks, and systems against ever changing attacks that target people and companies worldwide.
-
Risk Awareness: Comprehending cybersecurity domains facilitates the identification of possible risks and threats, allowing for proactive approaches to mitigate vulnerabilities and successfully safeguard vital digital assets.
-
Data Protection: By preventing breaches, leaks, or abuse that could endanger individuals, companies, or digital activities, cybersecurity expertise guarantees that sensitive data stays safe.
-
Career Growth: For professionals worldwide, mastering cybersecurity subjects opens up employment prospects, certifications, and responsibilities in risk management, SOCs, and IT security.
-
Compliance Requirements: Understanding security frameworks and standards guarantees that businesses adhere to rules, stay out of trouble, and keep stakeholders' and consumers' trust.
-
Threat Response: Understanding cybersecurity domains increases corporate resilience against contemporary digital threats, decreases downtime, and improves responsiveness to cyberattacks.
Spending time learning about cybersecurity domains improves careers, builds defenses, and highlights the importance of cybersecurity to safeguarding our interconnected world.
Understanding the Core Cybersecurity Domains
Firewalls and antivirus software are no longer the only aspects of cybersecurity. It covers a wide range of topics, from cloud architecture to human psychology. Let's examine the ten domains that you must become proficient in.
1. Security and Risk Management
The foundation of all cybersecurity procedures is security and risk management. It entails identifying the risks to your systems and putting mitigation strategies in place.
Key Concepts:
-
CIA Triad: The three pillars of cybersecurity are availability, integrity, and confidentiality.
-
Risk Assessment: Determine the resources, possible risks, weaknesses, and opportunities for exploitation.
-
Security Policies & Procedures: Provide rules for administrators, developers, and users.
-
Compliance Standards: Regulations like GDPR and CCPA, as well as frameworks like NIST and ISO 27001, guarantee that businesses adhere to industry and legal standards.
By ensuring that cybersecurity decisions are proactive rather than reactive, effective risk management enables organizations to reduce the probability and impact of cyber incidents.
2. Asset Security
Ensuring confidentiality, integrity, and availability while preventing unauthorized access, loss, or misuse of all digital and physical assets is the goal of asset security for a company.
Topics to Consider:
-
Data Classification: Recognizing sensitive data and assigning a priority label to it.
-
Encryption & Masking: Safeguarding information when it's in transit and at rest.
-
Data Lifecycle Management: Responsible data management, from generation to safe erasure.
-
Cloud Security: Protecting cloud-based assets requires the implementation of appropriate security controls, since cloud usage is at an all-time high.
Organizations can efficiently prioritize the protection of critical data, limit vulnerabilities, reduce potential attack surfaces, and increase overall resilience against cyber threats by concentrating on asset security.
3. Security Architecture and Engineering
While security engineering uses workable techniques to put safeguards in place, guaranteeing security across networks, applications, and infrastructure, security architecture develops an organized blueprint for creating secure systems.
Key Elements:
-
Secure System Design: Instead of including security as an afterthought, do so from the beginning.
-
Secure Software Development: Integrate security into development pipelines by implementing DevSecOps techniques.
-
Security Models: To direct access controls, use models such as Bell-LaPadula or Biba.
-
Emerging Approaches: Secure network architecture is being redefined by Zero Trust Architecture and SASE (Secure Access Service Edge).
Security engineering helps businesses avoid breaches and function safely in a changing cyber threat landscape by fortifying systems against attacks, preserving data integrity, and guaranteeing resilience.
4. Communication and Network Security
Since networks are the foundation of digital communication, they need strong security measures to safeguard data flow, stop intrusions, and preserve availability, confidentiality, and integrity across all systems.
Essentials of Network Security:
-
Common Threats: Phishing, DDoS attacks, ransomware, and Man-in-the-Middle attacks.
-
Network Protection Tools: Firewalls, IDS/IPS, VPNs, and segmentation techniques.
-
Secure Protocols: TLS, HTTPS, SSH, and modern encryption standards.
-
Wireless and IoT Security: Protecting devices beyond traditional IT infrastructure.
In an increasingly connected world, a robust network security policy protects sensitive data, stops illegal access, lessens cyberattacks, and guarantees dependable, continuous communication for businesses and consumers.
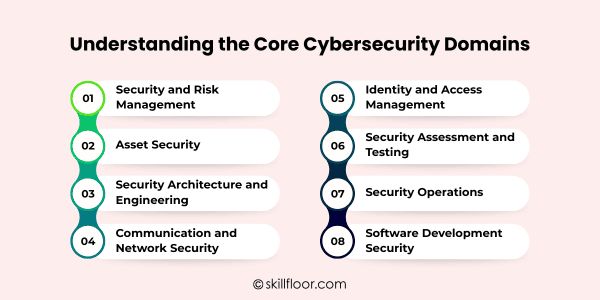
5. Identity and Access Management (IAM)
IAM is a crucial component of cybersecurity domains for corporate safety because it guarantees that the appropriate people have access to the correct resources at the right time.
IAM Fundamentals:
-
Authentication vs. Authorization: Confirming identity vs. granting permissions.
-
Single Sign-On (SSO) & Multi-Factor Authentication (MFA): Enhancing user security while maintaining usability.
-
Privileged Access Management (PAM): Protecting accounts with elevated privileges.
-
Identity Lifecycle: Managing onboarding, role changes, and offboarding securely.
In order to increase overall digital protection and operational resilience, effective IAM reduces internal threats, enforces appropriate permissions, and guarantees users may safely access only necessary systems.
6. Security Assessment and Testing
An essential component of cybersecurity domains for proactive defense, security assessment and testing assist firms in identifying vulnerabilities before attackers exploit them.
Core Practices:
-
Vulnerability Assessments: Scan systems for known weaknesses.
-
Penetration Testing: Ethical hacking to find exploitable vulnerabilities.
-
Red Teaming vs. Blue Teaming: Offensive vs. defensive security exercises.
-
Automated vs. Manual Testing: Combining tools and human expertise for comprehensive coverage.
Organizations can lower risk and increase overall resilience against emerging cyberattacks by using continuous testing to enhance security, identify threats early, and respond appropriately.
7. Security Operations
Daily monitoring, threat detection, and administration are all part of security operations, which are crucial to cybersecurity domains in order to safeguard systems and successfully handle incidents.
Key Activities:
-
Security Monitoring: Identifying problems and taking immediate action.
-
SIEM & SOAR Platforms: Automating the gathering, processing, and response processes of data.
-
Threat Intelligence: Collecting useful information to foresee attacks.
-
Incident Response & SOCs: Successfully anticipating, identifying, and reducing dangers.
Strong security measures limit harm, shorten attacker stay times, and guarantee quick incident response, preserving organizational resilience and protecting vital digital assets.
8. Software Development Security (Application Security)
Since programs serve as the primary user interface, protecting them with contemporary cybersecurity technologies guarantees protection against vulnerabilities during the stages of creation, testing, and deployment.
Important Areas:
-
Secure Coding Practices: Avoiding vulnerabilities listed in OWASP Top 10.
-
Testing Approaches: SAST (Static), DAST (Dynamic), and IAST (Interactive).
-
CI/CD Security Integration: Automating security in software pipelines.
-
Mobile & Web Application Security: Addressing platform-specific threats and vulnerabilities.
Software security ensures safe digital services and a dependable user experience by preventing attackers from taking advantage of vulnerabilities, lowering breach risks, and bolstering organizational defenses.
Other Specialized Cybersecurity Domains
Specialized fields cover advanced threat management, compliance, and emerging technologies in addition to the traditional cybersecurity domains. Modern, all-encompassing security solutions depend on these fields.
1. Cloud Security
Ensures safe operations in virtualized environments by utilizing access restrictions, encryption, and monitoring to safeguard cloud-based systems, apps, and data.
2. IoT Security
Protects networks and Internet of Things devices from assaults that target linked infrastructures, illegal access, and data leakage.
3. Mobile Security
Focuses on protecting communications, mobile devices, and apps from malware, phishing, and app-based vulnerabilities.
4. Threat Intelligence
Gathers, evaluates, and uses data about new risks to help firms foresee attacks and put proactive cybersecurity measures in place.
5. Industrial Control Systems (ICS) Security
Ensures industries like energy, manufacturing, and transportation stay safe and functional by defending vital infrastructure and operational technologies against cybersecurity threats.
6. Cryptography and Encryption
Protects data, upholds confidentiality, and guarantees integrity in communications and storage by using safe algorithms and encryption techniques.
7. Governance, Risk, and Compliance (GRC)
Ensures legal compliance and well-organized cybersecurity policies by coordinating security strategies with business objectives, legal requirements, and risk management procedures.
8. Identity and Privilege Management
Emphasizes privileged account management, access control, and sophisticated identity verification for improved organizational security.
9. Incident Response and Forensics
Focuses on identifying, evaluating, and reacting to cyber events while obtaining information for inquiries and strengthening defenses going forward.
Ensures the security of corporate systems by shielding individual devices—such as laptops, desktop computers, and mobile endpoints—from ransomware, malware, and illegal access.
Emerging Trends and the Future of Cybersecurity
Cybersecurity's future is changing quickly. In a world that prioritizes digitalization, organizations must adjust to new technologies, threats, and tactics in order to maintain security.
-
AI-Driven Security Solutions: AI substantially improves threat detection, automates responses, and fortifies defenses inside contemporary cybersecurity domain strategies.
-
Quantum Computing and Cryptography: Current encryption is challenged by quantum computing, necessitating the adoption of improved cryptography by companies in order to effectively safeguard sensitive data.
-
Cybersecurity for Critical Infrastructure: Energy grid, transportation, and smart city protection tackles operational hazards and sophisticated cybersecurity domain difficulties.
-
Preparing for Next-Generation Threats: Resilience against changing digital threats is ensured by anticipating ransomware, IoT vulnerabilities, and AI attacks.
-
Integration of Emerging Technologies: Threat management is enhanced and overall cybersecurity operations are strengthened when AI, blockchain, and cloud solutions are combined.
The future of cybersecurity necessitates ongoing innovation and flexibility, underscoring the significance of cybersecurity in protecting vital digital systems, networks, and data from more complex worldwide attacks.
Understanding and learning cybersecurity domains gives you the tools to stay safe in a digital world that is always changing. You can lower risks for your company and yourself by learning how to secure data, networks, and devices. These domains assist managers and IT specialists alike in anticipating threats before they materialize. Defending against assaults is made easier by using the appropriate tools, maintaining current knowledge of developing technologies, and adopting sound security practices. By concentrating on cybersecurity domains, you can enjoy technology without always worrying about dangers, maintain system security, and gain confidence.