In today's digital age, cybercrime is on the rise, and organizations are increasingly aware of the need for cybersecurity. This has resulted in a high demand for professionals trained in cybersecurity. The Cyber Security Course in Reading is designed to provide individuals with the necessary skills and knowledge to protect organizations from cyber threats. The Cyber Security Course in Reading covers various topics, including cybersecurity principles, risk management, network security, and cryptography. The course also provides hands-on training in various cybersecurity tools, techniques, and methodologies. The cybersecurity principles covered in the course include security frameworks, security governance, and security culture. Professionals trained in cybersecurity principles can effectively lead and manage cybersecurity teams and develop security solutions that align with an organization's goals and objectives. Risk management is another important component of the Cyber Security Course in Reading. The course covers the various risk assessment techniques, risk management best practices, and regulatory compliance. By understanding risk management principles, cybersecurity professionals can identify potential risks and develop strategies to mitigate them effectively. The course provides in-depth training in network security, including network architecture, firewalls, intrusion detection and prevention, and virtual private networks (VPNs). These skills enable cybersecurity professionals to design and manage secure networks that protect an organization's data and assets from cyber threats. The Cyber Security Course in Reading also covers cryptography, which is the science of secure communication. Cryptography algorithms and methodologies are used to secure data in transit and at rest. Cybersecurity professionals trained in cryptography can develop secure communication systems, secure data storage, and ensure the confidentiality and integrity of data. The hands-on training provided in the Cyber Security Course in Reading includes hands-on exercises and simulations of real-world cyber threats. This training enables students to gain practical experience in identifying, diagnosing, and resolving cyber threats. The course also includes training in security tools and techniques such as threat intelligence, penetration testing, and vulnerability assessment. The course also covers regulatory compliance, including GDPR, PCI-DSS, and ISO 27001. Compliance with these regulations is crucial for organizations that handle sensitive data. Cybersecurity professionals trained in regulatory compliance can ensure that an organization's cybersecurity policies align with the regulatory requirements and mitigate the risk of regulatory non-compliance. In conclusion, the Cyber Security Course in Reading is an excellent choice for anyone interested in pursuing a career in cybersecurity. The course covers a wide range of topics, including cybersecurity principles, risk management, network security, cryptography, and regulatory compliance. The hands-on training provided in the course enables students to gain practical experience and develop skills in cybersecurity tools and techniques. By completing the Cyber Security Course in Reading, students can acquire the necessary knowledge and skills to protect organizations from cyber threats and advance their careers in cybersecurity.

₹60,000


Hurry Up!
Limited seats call us now for amazing discounts on Ethical Hacking Courses course

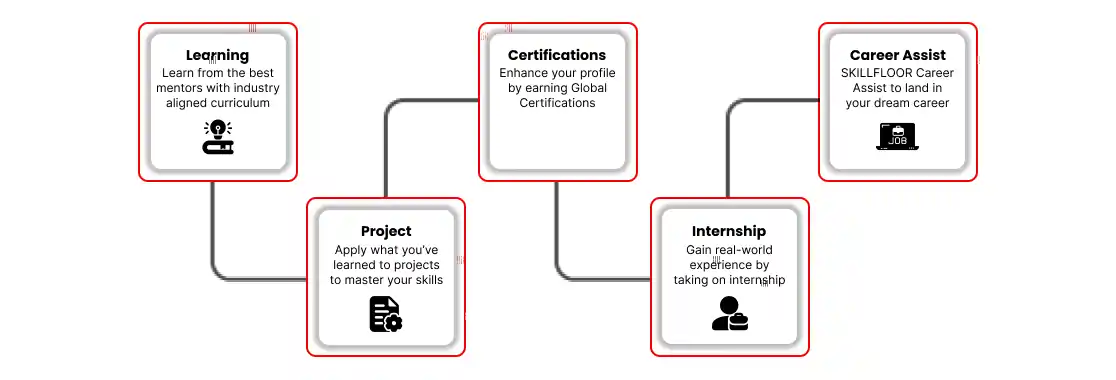

Skillfloor is a Government-Recognized Skill Development Institute under Startup India (DPIIT), offering career-focused certification programs in Analytics, Artificial Intelligence (AI), Data Science, Digital Marketing, SEO, and related domains. As one of India's largest training institutes, our courses emphasize hands-on projects, expert mentorship, and skills aligned with real hiring needs. With flexible learning options - online, offline, and hybrid, plus 100% scholarships for selective students, we make quality, job-ready education accessible.
Explore the program that aligns with your goals and take the next step with Skillfloor.


- Overview of Cyber Security Concepts
- Types of Cyber Threats (Malware, Ransomware, Phishing, etc.)
- Cybersecurity Frameworks and Standards (NIST, ISO 27001)
- The Role of Cyber Security in Organizations
- Key Cyber Security Terminology (Vulnerabilities, Risks, Threats)
- Understanding Networking Basics (IP, DNS, TCP/IP)
- Network Security Devices: Firewalls, Routers, and Switches
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
- Secure Network Design and Segmentation
- Virtual Private Networks (VPNs) and Secure Communication Protocols
- Confidentiality, Integrity, and Availability (CIA Triad)
- Risk Management Processes (Assessment, Mitigation, Response)
- Types of Security Controls (Preventive, Detective, Corrective)
- Security Policies and Standards (ISO, NIST)
- Security Audits and Compliance Requirements (SOX, GDPR)
- Basics of Cryptography: Symmetric vs Asymmetric Encryption
- Public Key Infrastructure (PKI) and Digital Certificates
- Common Cryptographic Algorithms (AES, RSA, ECC)
- Digital Signatures and Certificates
- Hashing Algorithms and Their Applications (SHA, MD5)
- Common Web Application Vulnerabilities (SQL Injection, XSS)
- OWASP Top 10: Key Vulnerabilities and Mitigation
- Secure Software Development Lifecycle (SSDLC)
- Web Application Firewalls (WAF) and Their Role
- Authentication and Session Management Best Practices
- Phases of Penetration Testing: Reconnaissance, Scanning, Exploitation
- Vulnerability Scanning and Risk Assessment
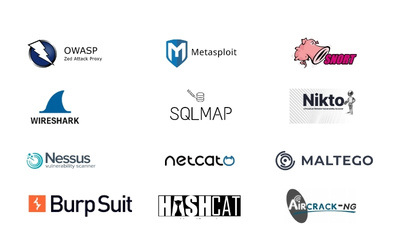
- Tools for Ethical Hacking: Nmap, Metasploit, Burp Suite
- Social Engineering Attacks and Mitigation
- Writing Penetration Testing Reports and Documentation
- Incident Response Lifecycle: Identification, Containment, Eradication
- Incident Response Plans and Team Structure
- Forensic Analysis of Cyber Incidents
- Collecting and Preserving Digital Evidence
- Using SIEM (Security Information and Event Management) for Monitoring
- Understanding Cloud Computing Models (IaaS, PaaS, SaaS)
- Security Challenges in the Cloud: Data Breaches, Misconfigurations
- Shared Responsibility Model in Cloud Security
- Cloud Security Best Practices (Encryption, Access Control)
- Securing Cloud Platforms: AWS, Microsoft Azure, Google Cloud
- Authentication Mechanisms: Passwords, Biometric, 2FA, MFA
- Role-Based Access Control (RBAC) vs. Attribute-Based Access Control (ABAC)
- Single Sign-On (SSO) and Federation
- Privileged Access Management (PAM)
- Identity and Access Management Solutions (Okta, Azure AD)
- Overview of Data Protection Laws (GDPR, HIPAA, PCI-DSS)
- Cybersecurity Compliance Frameworks (NIST, CIS Controls)
- Data Privacy Regulations and Their Implications
- Legal Requirements for Incident Reporting and Data Breach Notifications
- Understanding Cyber Liability Insurance and Legal Risks