CYBER SECURITY TRAINING IN RANCHI
-

-
(12639 Reviews)
-
Exciting Career Opportunities: Discover the top job openings in Ranchi’s cyber security industry. Prepare for in-demand roles like security analyst or ethical hacker.
-
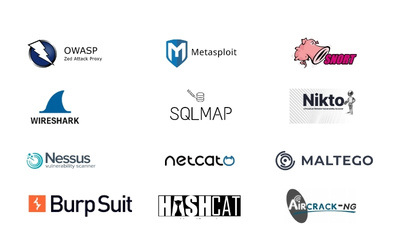
Key Skills for Success: Learn essential skills such as network security, threat detection, and risk management to safeguard businesses online.
-
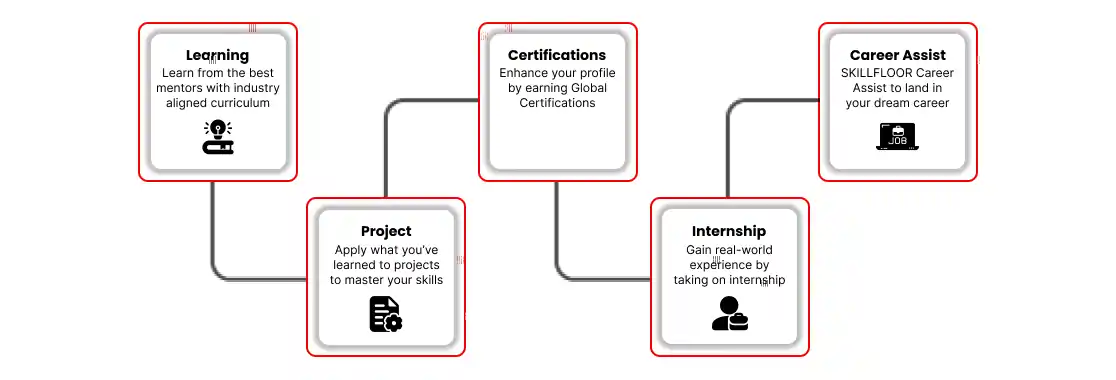
Practical Training Experience: Get valuable real-world experience through internships with leading companies. Enhance your skills and confidence to build a successful cyber security career.