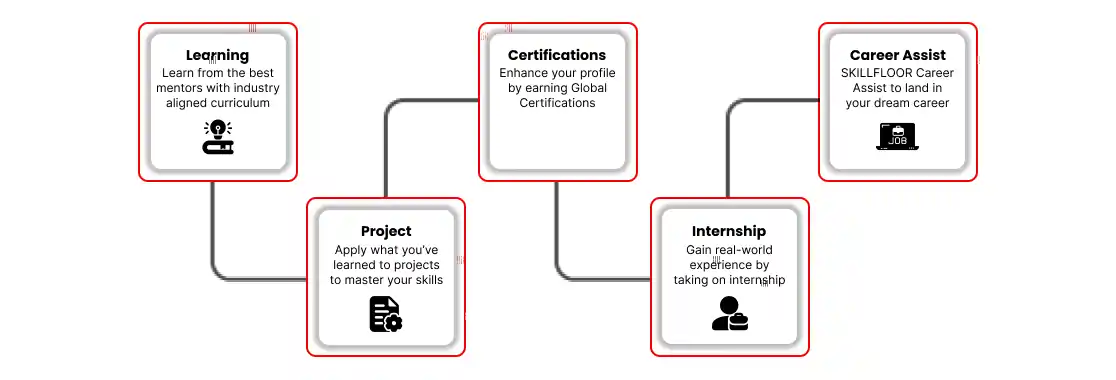
Before exploring the course details, it’s important to understand what makes this program stand out. Skillfloor’s Certified Ethical Hacking Professional Course is designed to provide practical cybersecurity learning, real-world project experience, and complete career support in one program. Here are the top reasons why this course is the right choice for building a successful career in ethical hacking and cybersecurity:
1. Explore Ethical Hacking from Fundamentals to Advanced Techniques
At Skillfloor, you’ll learn ethical hacking with a strong focus on practical cybersecurity skills and real-world security testing. This course is designed to help you understand modern cybersecurity practices and master the tools used by ethical hacking professionals.
Core Ethical Hacking Skills You Will Learn
-
Network Security: Learn how networks operate and understand techniques to secure systems, monitor traffic, and prevent cyber threats effectively.
-
Penetration Testing: Understand how ethical hackers identify and test system vulnerabilities using real-world hacking methods. With cyberattacks rising by nearly 38% globally, penetration testing skills are in high demand.
-
Web Application Security: Learn to detect and prevent website vulnerabilities such as SQL injection, XSS attacks, and authentication-related security flaws.
-
Vulnerability Assessment: Develop skills to identify, analyze, and manage cybersecurity risks using modern vulnerability assessment tools and security practices. Over 60% of organizations now focus on proactive security testing to reduce cyber risks.
-
Cybersecurity Fundamentals: Build strong knowledge in cybersecurity concepts, malware protection, system security, and risk management used in modern organizations.
-
Ethical Hacking Tools: Gain hands-on experience with industry-standard tools like Kali Linux, Wireshark, Nmap, Metasploit, Burp Suite, and Nessus for security testing.
-
Live Cybersecurity Projects: Work on real-time cybersecurity projects and simulated hacking environments to apply your practical skills in real-world scenarios. Companies highly value candidates with project-based cybersecurity experience.
-
Industry-Focused Practical Learning: Learn through live training sessions, practical assignments, and hands-on activities designed to prepare you for real cybersecurity job roles.
2. Master Essential Skills for Ethical Hacking Roles
Develop practical, job-ready cybersecurity skills that are highly demanded across IT companies, cybersecurity firms, startups, and enterprises. Skillfloor helps you gain the confidence to handle real-world security challenges effectively.
Practical Cybersecurity Skills You Will Develop
-
Network Security Management: Learn to secure networks, monitor traffic, and identify system vulnerabilities.
-
Penetration Testing Skills: Test systems and applications for security weaknesses using ethical hacking techniques.
-
Vulnerability Assessment: Identify, analyze, and manage cybersecurity risks using security tools and practices.
-
Web Application Security: Detect and prevent vulnerabilities like SQL injection, XSS attacks, and authentication flaws.
-
Security Monitoring & Analysis: Monitor systems, analyze threats, and improve cybersecurity protection strategies.
-
Ethical Hacking Tools Handling: Gain hands-on experience with Kali Linux, Wireshark, Nmap, Metasploit, and Burp Suite.
-
Cybersecurity Reporting: Prepare security reports and recommend solutions for identified vulnerabilities.
-
Real-Time Project Execution: Work on live cybersecurity projects and practical security testing scenarios.
3. Structure of Ethical Hacking Course Fee in 2026
-
Basic/Short-Term Cybersecurity Courses (1–3 Months): ₹10,000–₹35,000
-
Advanced Ethical Hacking Certificate Courses (3–6 Months): ₹20,000–₹150,000
-
Diploma & Professional Cybersecurity Programs (6–12 Months): ₹80,000–₹400,000
-
Executive & Master-Level Cybersecurity Programs (12–18 Months): ₹300,000–₹800,000
Skillfloor Course Fee Structure
Skillfloor’s Certified Ethical Hacking Professional Course is competitively priced at ₹14,900, offering practical cybersecurity training with live classes, hands-on projects, internships, and career support, making it a cost-effective choice for students, freshers, and working professionals.
-
Certified Ethical Hacking Professional: ₹14,900 – 6 weeks of live training + 6 weeks of internship.
-
Certified Penetration Testing Professional: ₹14,900 – 6 weeks of live training + 6 weeks of internship.
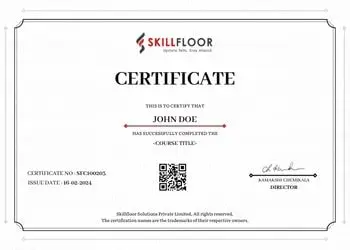
Certifications You Earn
-
Skillfloor Certified Ethical Hacking Professional Certificate
-
Certifications accredited by ICFQ, NASSCOM, and FutureSkills Prime
-
Additional certifications in ethical hacking, penetration testing, vulnerability assessment, web security, and cybersecurity tools
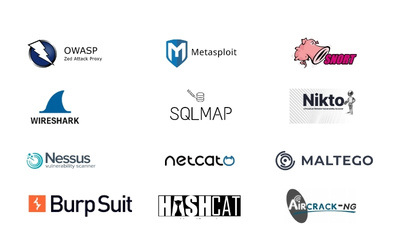
4. Tools You Will Learn: Modern Ethical Hacking & Cybersecurity Tools
Get hands-on experience with industry-standard cybersecurity and ethical hacking tools used by security professionals to identify vulnerabilities, secure systems, and perform penetration testing.
-
Network Scanning & Monitoring Tools: Wireshark, Nmap, and Angry IP Scanner for network analysis, traffic monitoring, and vulnerability detection.
-
Penetration Testing Tools: Metasploit, Burp Suite, Hydra, and John the Ripper for security testing, password auditing, and penetration testing activities.
-
Vulnerability Assessment Tools: Nessus, OpenVAS, and Nikto for identifying system vulnerabilities and improving cybersecurity protection.
-
Web Application Security Tools: Burp Suite, OWASP ZAP, SQLmap for testing web applications and detecting common security flaws.
-
Operating Systems & Security Platforms: Kali Linux and Parrot OS for performing ethical hacking, penetration testing, and cybersecurity tasks.
-
Password Cracking & Security Testing: Aircrack-ng, Hashcat, and Hydra for password analysis and wireless security testing.
-
AI-Powered Cybersecurity Tools: Learn how AI tools like ChatGPT, Gemini, and cybersecurity automation platforms are used for threat analysis, security research, vulnerability reporting, and cybersecurity workflow automation.
5. Outcomes You Can Expect from This Ethical Hacking Course
By the end of this course, you will not only understand ethical hacking concepts but also confidently apply cybersecurity skills in real-world situations. The program is designed to help beginners build strong practical knowledge and become industry-ready cybersecurity professionals.
Key Achievements
-
You will learn how to identify security vulnerabilities, protect systems, and handle cybersecurity challenges using modern ethical hacking techniques, followed by organizations worldwide.
-
You will gain practical experience in penetration testing and vulnerability analysis to find and fix security weaknesses in networks, applications, and digital systems.
-
You will develop the ability to secure websites and applications by detecting threats such as SQL injection, XSS attacks, and authentication vulnerabilities.
-
You will work with industry-standard cybersecurity tools including Kali Linux, Wireshark, Metasploit, Burp Suite, and Nessus for real-time security testing and analysis.
-
You will also understand how to assess cybersecurity risks, create professional security reports, and recommend solutions to strengthen overall system security and protection.
6. Course Highlights & Career Support
Skillfloor’s Certified Ethical Hacking Professional Course is designed not just to teach you cybersecurity skills, but to support you throughout your complete career journey, from learning ethical hacking concepts to getting placed in the cybersecurity industry.
-
100% Placement Support & Career Assistance: You receive complete career support that goes beyond training. This includes 100% placement assistance, personalized career guidance, mock interviews, and professional resume building. You’ll be guided on how to confidently present your cybersecurity skills, crack interviews, and connect with hiring companies in the ethical hacking and cybersecurity industry.
-
Industry-Recognized Certifications: Upon completion, you will earn a Skillfloor Certified Ethical Hacking Professional Certification along with an IIDMC certification accredited by FutureSkills Prime and NASSCOM. These certifications are LinkedIn-shareable, helping you build a strong professional presence and gain credibility with recruiters and employers.
-
Internship with Real-World Experience: A key highlight of the program is the project-based internship, where you will work on real-time ethical hacking and cybersecurity projects. With a 1-student–1-project approach, you gain practical exposure by handling real security testing scenarios, giving you hands-on experience that employers highly value.
-
Structured Course Duration: The program is designed for effective learning and practical exposure, with 6 weeks of intensive live training followed by 6 weeks of internship. This structure ensures you not only learn cybersecurity concepts but also apply them in real-world security environments.
-
Flexible Learning Modes: To suit different learning needs, Skillfloor offers online, offline, and hybrid training options. This flexibility allows you to learn at your own pace while balancing studies or work commitments.
-
Complete Career Services: In addition to placement support, you’ll receive end-to-end career services, including portfolio development, LinkedIn profile optimization, and expert mentoring. These services ensure you are fully prepared to enter the cybersecurity job market with confidence and stand out among other candidates.
7. Role of Ethical Hacking: Future-Ready Skills
Ethical hacking is becoming one of the most important skills in today’s digital world, helping organizations identify security weaknesses before cybercriminals can exploit them. Modern businesses rely on ethical hackers to protect sensitive information, secure networks, and strengthen digital systems against growing cyber threats.
You will discover useful ethical hacking techniques in this course that can be used to test system security, find vulnerabilities, and enhance overall network, application, and website protection. Additionally, you will comprehend how ethical hackers do security evaluations and penetration tests in actual settings.
In areas including network security, online application security, vulnerability assessment, password security testing, and ethical hacking tools, the program emphasizes practical learning. These useful abilities enable students to comprehend contemporary ethical hacking techniques used by businesses today and confidently solve actual security concerns.
Strong employment opportunities in IT companies, startups, cybersecurity firms, and corporate organizations are made possible by the high value placed on ethical hacking talents across industries. Ethical hacking provides good career progression, real-world learning opportunities, and long-term job stability in the technology industry, which is in line with the growing demand for security specialists.
8. Job Roles, Salaries & Growth Opportunities
Skillfloor’s Certified Ethical Hacking Professional Course prepares you for some of the most in-demand ethical hacking and security testing roles, offering strong salary potential and long-term career growth opportunities.
- Ethical Hacking Executive: As an Ethical Hacking Executive, you’ll perform security testing, identify vulnerabilities, and help organizations strengthen their system security. This is an ideal entry-level role for gaining practical ethical hacking experience.
Salary: ₹3 – ₹6 LPA
- Penetration Tester: In this role, you’ll test networks, applications, and systems for security weaknesses using ethical hacking techniques and penetration testing tools.
Salary: ₹4 – ₹8 LPA
- Web Application Security Analyst: A Web Application Security Analyst focuses on identifying and fixing website security vulnerabilities such as SQL injection, XSS attacks, and authentication flaws.
Salary: ₹4 – ₹9 LPA
- Vulnerability Assessment Analyst: This role involves analyzing systems for security risks, preparing security reports, and helping organizations improve protection against cyber threats.
Salary: ₹5 – ₹10 LPA
Career Growth Opportunities
Strong and quickly growing job prospects in cybersecurity, IT, startups, and enterprise organizations are provided by ethical hacking. In today's technological market, competent ethical hackers are highly valued due to the growing amount of cyber dangers.
-
High demand for ethical hackers across multiple industries and organizations.
-
Possibilities for employment in security consulting, IT, and cybersecurity enterprises.
-
Globally, remote cybersecurity initiatives and freelancing are expanding quickly.
-
With experience, you can rise in your profession and earn more money in positions like Senior Penetration Tester, Security Consultant, Cybersecurity Analyst, or Ethical Hacking Lead.
9. Skillfloor Ethical Hacking Course List
-
Certified Ethical Hacking Associate
-
Certified Ethical Hacking Professional
-
Certified Penetration Testing Professional
10. Topics Covered: From Basics to Real-World Ethical Hacking Practice
Skillfloor’s Certified Ethical Hacking Professional Course is structured to provide complete hands-on learning, combining core cybersecurity fundamentals with real-world ethical hacking skills and practical security testing experience.
-
Introduction to Ethical Hacking: Learn the basics of ethical hacking, cybersecurity concepts, and how attackers exploit systems and networks.
-
Network Security: Understand how networks operate and learn techniques to secure systems, monitor traffic, and detect vulnerabilities.
-
Penetration Testing: Perform controlled security testing to identify weaknesses in systems, applications, and networks using ethical hacking methods.
-
Web Application Security: Learn to detect vulnerabilities like SQL injection, XSS, and authentication flaws in websites and applications.
-
Vulnerability Assessment: Identify, analyze, and manage security risks using industry-standard tools and cybersecurity practices.
-
Password & System Security: Understand password attacks, system hardening techniques, and methods to strengthen overall security.
-
Ethical Hacking Tools: Gain hands-on experience with tools like Kali Linux, Wireshark, Nmap, Metasploit, Burp Suite, and Nessus.
-
Cybersecurity Reporting: Learn how to document vulnerabilities, prepare security reports, and suggest effective fixes.
-
Live Security Testing & Projects: Work on real-time hacking simulations and security scenarios to gain practical exposure.
-
Internship with Real-Time Practice: Gain hands-on experience through project-based learning with a 1-student–1-project approach, helping you apply ethical hacking skills in real environments.
This structured curriculum ensures you gain practical knowledge, real-world cybersecurity experience, and job-ready ethical hacking skills to build a successful career.
Skillfloor’s Certified Ethical Hacking Professional Course equips you with practical cybersecurity skills, real-world ethical hacking experience, and complete career support to succeed in today’s security-driven digital world. With live security projects, internship opportunities, and industry-recognized certifications, you become job-ready and confident to build a successful career in ethical hacking and cybersecurity.