CYBER SECURITY TRAINING IN KANPUR
-

-
(17810 Reviews)
-
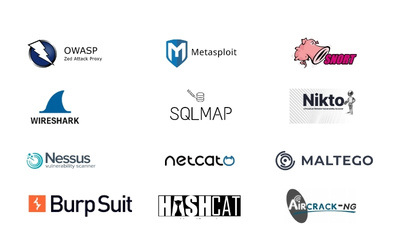
Skills: Gain key cybersecurity skills, such as protecting networks, ethical hacking, handling security incidents, and managing risks.
-
Career: Explore various career paths, such as becoming a cybersecurity analyst, penetration tester, security consultant, or network security engineer.
-
Syllabus: Understand topics like identifying threats, encryption, safe coding, security rules, and standards, and overall cybersecurity management in this detailed training program.