CYBER SECURITY TRAINING IN GUNTUR
-

-
(13074 Reviews)
-
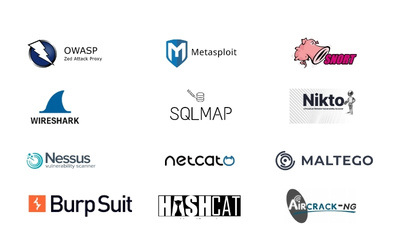
Skills: Gain essential cybersecurity skills, including network security, ethical hacking, incident response, and risk management.
-
Career: Explore diverse career opportunities in Guntur as a cybersecurity analyst, penetration tester, security consultant, or network security engineer.
-
Syllabus: Dive into a comprehensive training program covering threat detection, cryptography, secure coding practices, compliance frameworks, and cybersecurity management.