CYBER SECURITY TRAINING IN FARIDABAD
-

-
(19124 Reviews)
-
Career Opportunities: Discover a range of rewarding career opportunities in Faridabad's growing cyber security sector. Roles like security analyst and ethical hacker are in high demand, offering a promising career path for those looking to protect businesses from cyber threats.
-
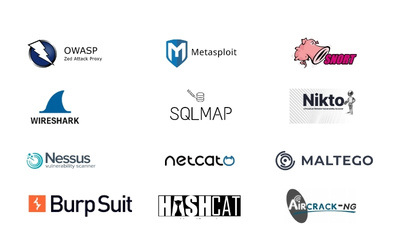
Essential Skills for Success: To thrive in the cyber security industry, you need key skills such as network security, ethical hacking, and cloud protection. By mastering these, you'll be equipped to tackle online threats and ensure the safety of businesses in the digital world.
-
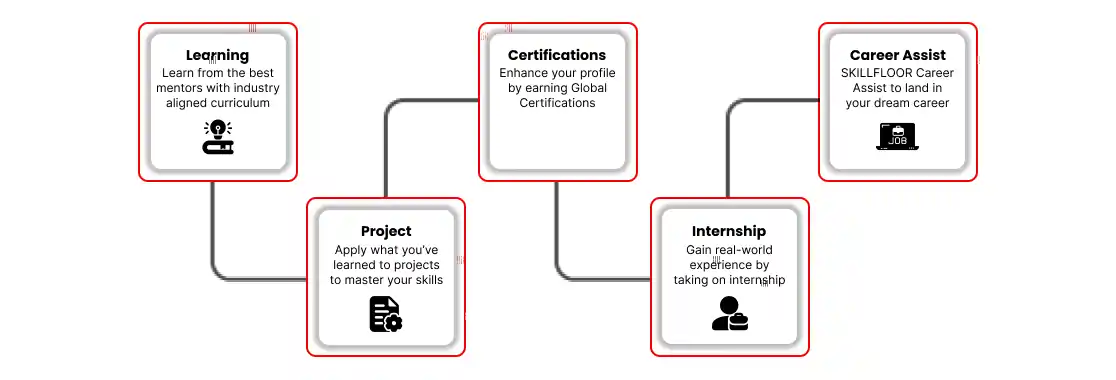
Practical Experience: Gain hands-on experience through internships with leading companies in Faridabad. This valuable experience will help you build your skillset and confidence, setting you up for a successful career in the dynamic field of cyber security.