Cybersecurity has become a crucial aspect of our digital world. Every day, news headlines are filled with reports of data breaches, cyber-attacks, and other security threats that affect both individuals and organizations. For this reason, cybersecurity has become one of the most in-demand professions globally, including in London, UK. London is one of the most significant cities in Europe with a thriving economy and a host of renowned universities and institutions. Therefore, it's an excellent place for cybersecurity enthusiasts to study and pursue cybersecurity careers. In this article, we will consider the cybersecurity courses in London and why they are essential. What is Cybersecurity, and why is it important? Cybersecurity is the practice of protecting computer systems, networks, and data from unauthorized access or attacks. This practice is vital because cybersecurity threats can cause significant business disruption, financial loss, and personal harm. In today's hyper-connected world, cybersecurity has never been more important as it affects individuals and organizations at all levels. Cybersecurity Courses in London London is the hub of the UK's cybersecurity industry, with various universities and colleges offering different cybersecurity courses. Some of the available cybersecurity courses in London include: 1. MSc Cyber Security and Data Governance - University of Greenwich 2. BSc Cyber Security and Networks - University of West London 3. MSc Cybersecurity - Imperial College London 4. MSC Information Security - Royal Holloway University of London 5. MSc Cyber Security and Management - University of Warwick These courses cover various aspects of cybersecurity such as cyber risk management, network security, security auditing, database security, and cryptography, among others. Why study Cybersecurity courses in London? 1. Excellent job opportunities As mentioned earlier, cybersecurity is an in-demand profession globally, including in London. Studying cybersecurity courses in London opens doors to various job opportunities in industries such as government agencies, financial institutions, and technology firms, among others. 2. Renowned universities and colleges London is home to some of the world's leading universities and colleges with a reputation for academic excellence and innovation. These institutions have a long history of producing world-class cybersecurity professionals, making London an excellent place to study. 3. Access to a network of cybersecurity professionals London has a booming cybersecurity community, bringing together cybersecurity professionals, academics, businesses, and government agencies. Therefore, studying cybersecurity courses in London provides access to a network of experts and professionals, offering invaluable knowledge, experience, and career insights. Conclusion Cybersecurity is an essential aspect of our digital world, and its importance is continuously growing. Studying cybersecurity courses in London provides an excellent opportunity for individuals interested in pursuing cybersecurity careers. Not only are there excellent job opportunities and renowned academic institutions, but there is also access to a vast network of cybersecurity professionals. Ultimately, cybersecurity courses equip students with in-demand skills needed to combat the ever-evolving cybersecurity threats.

₹60,000


Hurry Up!
Limited seats call us now for amazing discounts on Ethical Hacking Courses course


Skillfloor is a Government-Recognized Skill Development Institute under Startup India (DPIIT), offering career-focused certification programs in Analytics, Artificial Intelligence (AI), Data Science, Digital Marketing, SEO, and related domains. As one of India's largest training institutes, our courses emphasize hands-on projects, expert mentorship, and skills aligned with real hiring needs. With flexible learning options - online, offline, and hybrid, plus 100% scholarships for selective students, we make quality, job-ready education accessible.
Explore the program that aligns with your goals and take the next step with Skillfloor.


- Overview of Cyber Security Concepts
- Types of Cyber Threats (Malware, Ransomware, Phishing, etc.)
- Cybersecurity Frameworks and Standards (NIST, ISO 27001)
- The Role of Cyber Security in Organizations
- Key Cyber Security Terminology (Vulnerabilities, Risks, Threats)
- Understanding Networking Basics (IP, DNS, TCP/IP)
- Network Security Devices: Firewalls, Routers, and Switches
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
- Secure Network Design and Segmentation
- Virtual Private Networks (VPNs) and Secure Communication Protocols
- Confidentiality, Integrity, and Availability (CIA Triad)
- Risk Management Processes (Assessment, Mitigation, Response)
- Types of Security Controls (Preventive, Detective, Corrective)
- Security Policies and Standards (ISO, NIST)
- Security Audits and Compliance Requirements (SOX, GDPR)
- Basics of Cryptography: Symmetric vs Asymmetric Encryption
- Public Key Infrastructure (PKI) and Digital Certificates
- Common Cryptographic Algorithms (AES, RSA, ECC)
- Digital Signatures and Certificates
- Hashing Algorithms and Their Applications (SHA, MD5)
- Common Web Application Vulnerabilities (SQL Injection, XSS)
- OWASP Top 10: Key Vulnerabilities and Mitigation
- Secure Software Development Lifecycle (SSDLC)
- Web Application Firewalls (WAF) and Their Role
- Authentication and Session Management Best Practices
- Phases of Penetration Testing: Reconnaissance, Scanning, Exploitation
- Vulnerability Scanning and Risk Assessment
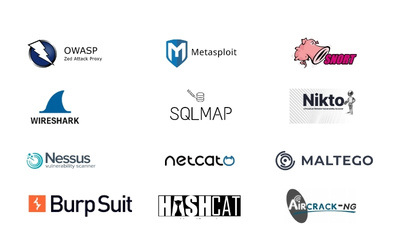
- Tools for Ethical Hacking: Nmap, Metasploit, Burp Suite
- Social Engineering Attacks and Mitigation
- Writing Penetration Testing Reports and Documentation
- Incident Response Lifecycle: Identification, Containment, Eradication
- Incident Response Plans and Team Structure
- Forensic Analysis of Cyber Incidents
- Collecting and Preserving Digital Evidence
- Using SIEM (Security Information and Event Management) for Monitoring
- Understanding Cloud Computing Models (IaaS, PaaS, SaaS)
- Security Challenges in the Cloud: Data Breaches, Misconfigurations
- Shared Responsibility Model in Cloud Security
- Cloud Security Best Practices (Encryption, Access Control)
- Securing Cloud Platforms: AWS, Microsoft Azure, Google Cloud
- Authentication Mechanisms: Passwords, Biometric, 2FA, MFA
- Role-Based Access Control (RBAC) vs. Attribute-Based Access Control (ABAC)
- Single Sign-On (SSO) and Federation
- Privileged Access Management (PAM)
- Identity and Access Management Solutions (Okta, Azure AD)
- Overview of Data Protection Laws (GDPR, HIPAA, PCI-DSS)
- Cybersecurity Compliance Frameworks (NIST, CIS Controls)
- Data Privacy Regulations and Their Implications
- Legal Requirements for Incident Reporting and Data Breach Notifications
- Understanding Cyber Liability Insurance and Legal Risks