Chicago is a hub for technology and digital innovation, which means that there are ample opportunities for individuals seeking to learn and work in the field of cyber security. A cyber security course in Chicago can provide you with specialized training in protecting digital assets and preventing cyber attacks, a skill set that is highly in-demand across industries. When looking for cyber security courses in Chicago, you will find a range of options from traditional universities and colleges to specialized technical schools and bootcamps. The courses vary in length, cost, and intensity, so it's important to do your research to find the best fit for your goals and needs. One respected institution offering cyber security training in Chicago is Northwestern University. Northwestern’s School of Professional Studies offers a part-time, online course in cyber security that’s designed for working professionals. The course spans six months and covers essentials, such as network security, cryptography, and data privacy. Graduates earn a certificate in Cybersecurity Risk Management. The program’s broad scope means that graduates can seek careers in many areas of cyber security, including risk management and compliance. Another option is a bootcamp-style training, which is increasingly popular with working professionals seeking to switch careers quickly. One organization, Evolve Security Academy, offers a 17-week bootcamp course in cyber security. The course is designed to give students hands-on experience with computer systems, data encryption, and digital forensics. Students also receive career counseling to help them prepare for the job market. If you're looking for shorter, more intensive cyber security training, there are a variety of options available as well. Springboard’s Cyber Security Career Track is a 6-month, mentor-guided programme that focuses on personalization and curriculum that enables you to learn by doing. This course's strengths are in its thorough curriculum, industry-relevant projects, and excellent career services. In addition to these formal training options, there's also a wealth of online learning resources for cyber security. Platforms such as Coursera, edX, and Udemy offer numerous online courses in cyber security, from basic awareness to certifications in specific skills. Overall, there are plenty of opportunities for individuals seeking to learn cyber security in Chicago, from traditional universities and bootcamps to online courses and specialized resources. The demand for cyber security professionals is only increasing as organizations face ever-evolving digital threats, making cyber security a promising career path for those looking for job security and a solid path to success in the technology field.

₹60,000


Hurry Up!
Limited seats call us now for amazing discounts on Ethical Hacking Courses course

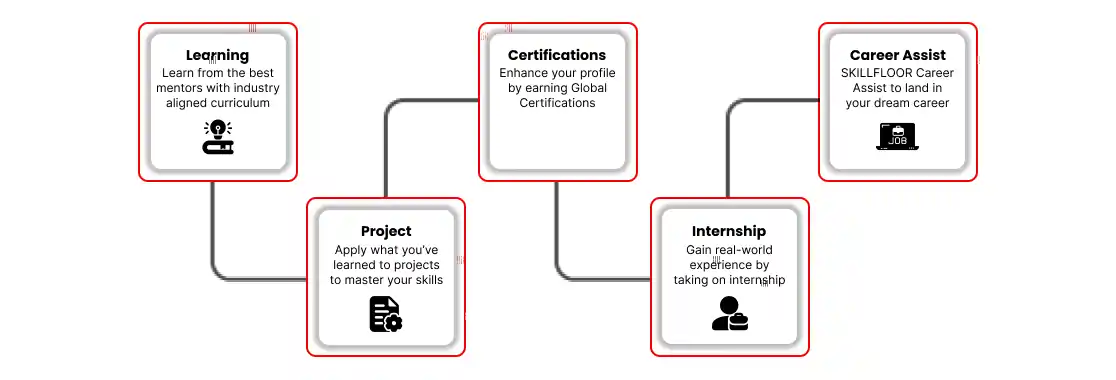

Skillfloor is a Government-Recognized Skill Development Institute under Startup India (DPIIT), offering career-focused certification programs in Analytics, Artificial Intelligence (AI), Data Science, Digital Marketing, SEO, and related domains. As one of India's largest training institutes, our courses emphasize hands-on projects, expert mentorship, and skills aligned with real hiring needs. With flexible learning options - online, offline, and hybrid, plus 100% scholarships for selective students, we make quality, job-ready education accessible.
Explore the program that aligns with your goals and take the next step with Skillfloor.


- Overview of Cyber Security Concepts
- Types of Cyber Threats (Malware, Ransomware, Phishing, etc.)
- Cybersecurity Frameworks and Standards (NIST, ISO 27001)
- The Role of Cyber Security in Organizations
- Key Cyber Security Terminology (Vulnerabilities, Risks, Threats)
- Understanding Networking Basics (IP, DNS, TCP/IP)
- Network Security Devices: Firewalls, Routers, and Switches
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
- Secure Network Design and Segmentation
- Virtual Private Networks (VPNs) and Secure Communication Protocols
- Confidentiality, Integrity, and Availability (CIA Triad)
- Risk Management Processes (Assessment, Mitigation, Response)
- Types of Security Controls (Preventive, Detective, Corrective)
- Security Policies and Standards (ISO, NIST)
- Security Audits and Compliance Requirements (SOX, GDPR)
- Basics of Cryptography: Symmetric vs Asymmetric Encryption
- Public Key Infrastructure (PKI) and Digital Certificates
- Common Cryptographic Algorithms (AES, RSA, ECC)
- Digital Signatures and Certificates
- Hashing Algorithms and Their Applications (SHA, MD5)
- Common Web Application Vulnerabilities (SQL Injection, XSS)
- OWASP Top 10: Key Vulnerabilities and Mitigation
- Secure Software Development Lifecycle (SSDLC)
- Web Application Firewalls (WAF) and Their Role
- Authentication and Session Management Best Practices
- Phases of Penetration Testing: Reconnaissance, Scanning, Exploitation
- Vulnerability Scanning and Risk Assessment
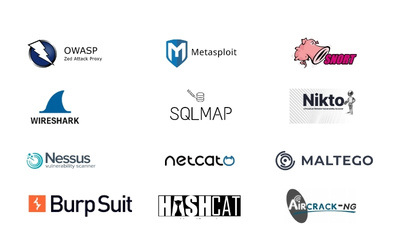
- Tools for Ethical Hacking: Nmap, Metasploit, Burp Suite
- Social Engineering Attacks and Mitigation
- Writing Penetration Testing Reports and Documentation
- Incident Response Lifecycle: Identification, Containment, Eradication
- Incident Response Plans and Team Structure
- Forensic Analysis of Cyber Incidents
- Collecting and Preserving Digital Evidence
- Using SIEM (Security Information and Event Management) for Monitoring
- Understanding Cloud Computing Models (IaaS, PaaS, SaaS)
- Security Challenges in the Cloud: Data Breaches, Misconfigurations
- Shared Responsibility Model in Cloud Security
- Cloud Security Best Practices (Encryption, Access Control)
- Securing Cloud Platforms: AWS, Microsoft Azure, Google Cloud
- Authentication Mechanisms: Passwords, Biometric, 2FA, MFA
- Role-Based Access Control (RBAC) vs. Attribute-Based Access Control (ABAC)
- Single Sign-On (SSO) and Federation
- Privileged Access Management (PAM)
- Identity and Access Management Solutions (Okta, Azure AD)
- Overview of Data Protection Laws (GDPR, HIPAA, PCI-DSS)
- Cybersecurity Compliance Frameworks (NIST, CIS Controls)
- Data Privacy Regulations and Their Implications
- Legal Requirements for Incident Reporting and Data Breach Notifications
- Understanding Cyber Liability Insurance and Legal Risks