Cybersecurity Framework Trends to Watch in 2026
Discover the top cybersecurity framework trends shaping 2026, including AI, Zero Trust, cloud security, compliance, and advanced cyber resilience strategies.

Cyber threats constantly change and expand. Today's enterprises face a wide range of security dangers, from ransomware attacks to intricate supply-chain breaches. As a result, cybersecurity frameworks have grown in significance. These frameworks are collections of rules that assist companies in comprehending, controlling, and lowering cyber threats in an organized manner.
Organizations can develop strong security procedures with the help of frameworks like the CIS Critical Security Controls, ISO/IEC 27001, and NIST Cybersecurity Framework. They offer precise instructions for identifying risks, safeguarding systems, spotting threats, handling incidents, and recovering from a cyberattack.
However, businesses' use of these frameworks is constantly increasing. New security issues are being brought about by emerging technologies like cloud computing, artificial intelligence, remote labor, and linked digital systems. Cybersecurity frameworks are also changing as a result of these developments. As 2026 approaches, a number of new developments are beginning to influence how businesses handle cybersecurity and lower risks.
Why Cybersecurity Frameworks Matter More Than Ever
Cybersecurity frameworks serve as a manual for creating robust security initiatives. They assist companies in identifying their risks, safeguarding critical systems, identifying threats early, responding to problems, and swiftly recovering from an incident.
Many organizations follow frameworks developed by international standards organizations like the International Organization for Standardization and reputable organizations like the National Institute of Standards and Technology. These frameworks provide businesses with best practices and explicit methods to enhance their cybersecurity.
These frameworks help companies answer critical questions:
-
Are we protecting our most important assets?
-
Can we detect attacks early enough?
-
Do we know how to respond when things go wrong?
-
Do we have the right processes in place to recover quickly after a cyber incident?
Many cybersecurity frameworks were created with a different digital environment in mind. The security environment has transformed as a result of modern technologies like cloud computing, artificial intelligence-driven attacks, and intricate supply chains, making 2026 a crucial year for how businesses approach cybersecurity frameworks.
Why Traditional Security Approaches Are Breaking
Several significant cyber incidents over the past decade have shown how interconnected contemporary digital systems are and how a single vulnerability can put thousands of businesses at serious risk.
The SolarWinds supply chain attack is a well-known example of how hackers hacked trusted software updates, showing how even reputable and experienced companies can be surprisingly vulnerable to advanced threats.
Today’s cyber risks include:
-
AI-powered phishing and social engineering
-
Sophisticated ransomware-as-a-service groups
-
Cloud misconfigurations
-
Third-party vendor vulnerabilities
-
Massive identity-based attacks
Attackers are always changing, but many organizations still rely on annual audits and unchanging frameworks. This growing disparity emphasizes the importance of cybersecurity, propelling frameworks to change and shape the following decade of digital defense.
Cybersecurity Framework Trends to Watch in 2026
1. Shift from Compliance-Driven to Risk-Driven Security
Organizations used cybersecurity frameworks as compliance checklists to pass audits for a long time. As businesses concentrate more on strengthening their actual security posture, this strategy is evolving.
Risk-based security strategies are currently the main emphasis of contemporary frameworks. This change is highlighted by the NIST Cybersecurity Framework 2.0, which places a strong emphasis on leadership accountability for managing significant cyber risks, governance, and risk management integration.
Organizations are now adopting practices such as:
-
Continuous risk assessment
-
Business-aligned cybersecurity strategies
-
Real-time threat monitoring
-
Risk prioritization based on asset value
This shift ensures that security investments directly support organizational objectives while reducing exposure to critical threats.
2. Integration of Zero Trust Architecture
Zero Trust Architecture is one of the fundamental cybersecurity ideas influencing contemporary frameworks. Users within networks were trusted by traditional security models, but contemporary attacks demonstrate that this strategy is no longer secure.
"Never trust, always verify" is the tenet of Zero Trust. Many firms have been encouraged to include Zero Trust principles in their cybersecurity frameworks by guidelines issued by the National Institute of Standards and Technology.
Key elements of Zero Trust include:
-
Continuous authentication and authorization
-
Identity-centric security controls
-
Least-privilege access policies
-
Network micro-segmentation
-
Continuous monitoring of user behavior
Organizations may drastically lower the risk of lateral movement attacks, credential compromise, and insider threats by integrating Zero Trust concepts into frameworks.
3. Greater Focus on Security Governance and Policy Management
A cybersecurity framework involves creating robust policies and procedures to guide cybersecurity practices. These policies outline the expected behaviors, responsibilities, and protocols for employees and stakeholders. Procedures provide step-by-step instructions for implementing security measures, incident response protocols, and risk mitigation strategies.
In order to guarantee that technical controls are uniformly implemented and security initiatives are successful throughout the company, effective governance establishes roles, allocates duties, and directs risk assessment and mitigation.
Key elements of security governance and policy management include:
-
Establishing clear cybersecurity policies aligned with business goals
-
Defining roles and responsibilities for security oversight
-
Regular policy review and updates to reflect evolving threats
-
Compliance monitoring and audit readiness
-
Integration of governance with risk management and operational processes
Cybersecurity frameworks that prioritize governance increase compliance, decrease errors, enhance responsibility, and guarantee uniform security procedures across the entire enterprise.
4. Emergence of Cloud-Native Security Frameworks
IT infrastructure has been transformed by cloud computing, and many businesses now employ hybrid or multi-cloud configurations. Traditional on-premise frameworks were not intended to address the increased security concerns brought forth by this change.
Industry associations like the Cloud Security Alliance developed frameworks like the Cloud Security Alliance Cloud Controls Matrix to address cloud-specific vulnerabilities, including misconfigurations and insecure APIs.
In 2026, cloud-focused framework adoption will continue to grow, with organizations emphasizing:
-
Secure cloud architecture design
-
Multi-cloud governance strategies
-
Infrastructure-as-Code security validation
-
Cloud workload protection
-
Continuous configuration monitoring
These practices help organizations maintain visibility and control across complex cloud ecosystems.
5. DevSecOps Becoming a Core Framework Component
Although conventional security procedures frequently impede development, software development is now a crucial component of digital transformation. Businesses require safer, quicker methods for developing and implementing software.
Many are implementing DevSecOps, which incorporates security into the development process, to address this. Organizations are guided on secure coding and best practices by frameworks such as the Secure Software Development Framework (SSDF).
Key DevSecOps practices include:
-
Automated vulnerability scanning
-
Security testing within CI/CD pipelines
-
Static and dynamic code analysis
-
Secure dependency management
-
Developer security training
By embedding security early in the development process, organizations can detect vulnerabilities before software reaches production environments.
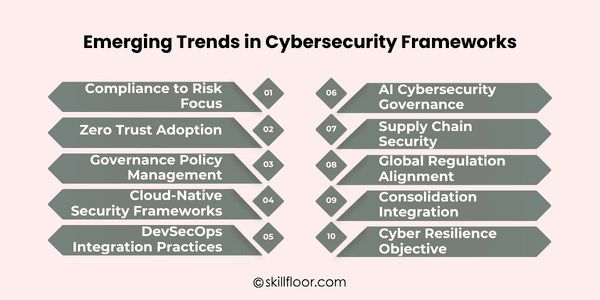
6. AI-Driven Cybersecurity Governance
Cybersecurity operations are rapidly changing due to artificial intelligence. AI technologies are helping companies evaluate enormous amounts of security data more efficiently, from threat detection to automated response.
AI-assisted security management is starting to be included in cybersecurity frameworks' recommendations.
AI can support framework implementation through:
-
Behavioral anomaly detection
-
Automated threat intelligence analysis
-
Predictive risk modeling
-
Security orchestration and automated response
Organizations must manage risks like data poisoning and model manipulation as AI adoption increases, underscoring the importance of cybersecurity technologies as future frameworks incorporate AI governance and risk controls.
7. Supply Chain Security Becoming a Priority
Attacks on supply chains have exposed significant flaws in digital ecosystems. In order to obtain access to other companies downstream, cybercriminals frequently target reliable vendors or software providers.
The SolarWinds supply chain attack, which affected thousands of people globally, is a prominent example. As a result, frameworks now place more emphasis on software supply chain security and third-party risk management.
Organizations are increasingly implementing practices such as:
-
Vendor security assessments
-
Third-party risk scoring
-
Software Bill of Materials (SBOM) adoption
-
Continuous monitoring of supplier security posture
-
Secure software distribution processes
Organizations can lower the risk of cascading cyber incidents across partner ecosystems by strengthening supply chain security measures.
8. Stronger Alignment with Global Regulations
Nowadays, cybersecurity is more than simply a technical issue; many sectors are subject to stringent rules. Governments all across the world are enacting stricter regulations to safeguard sensitive information, organizational systems, and vital infrastructure.
Frameworks are increasingly aligning with regulatory standards such as:
-
General Data Protection Regulation
-
Digital Operational Resilience Act
-
NIS2 Directive
This alignment makes it easier for businesses to manage compliance by mapping cybersecurity controls to legal obligations.
Cybersecurity frameworks will remain the cornerstone of governance, risk, and compliance (GRC) efforts as regulatory pressure mounts.
9. Framework Consolidation and Integration
Managing several cybersecurity frameworks at once is a challenge for many firms. For instance, a business may have to adhere to both national and industry-specific regulations and ISO standards.
Organizations are increasingly using framework cross-mapping and consolidation techniques to address this issue.
This approach involves:
-
Mapping controls between frameworks
-
Creating unified security policies
-
Implementing integrated risk dashboards
-
Using governance platforms to manage multiple standards
To simplify security governance, for instance, enterprises frequently link controls between ISO/IEC 27001 and the NIST Cybersecurity Framework.
Organizations can minimize redundancy, streamline audits, and keep a uniform security posture by implementing framework consolidation.
10. Cyber Resilience as the Ultimate Objective
Organizations today acknowledge the inevitable nature of cyber disasters, even though prevention is still crucial. Consequently, the emphasis on cyber resilience in contemporary frameworks is growing.
The goal of cyber resilience is to make sure that businesses can function even in the face of cyber threats.
Key resilience practices include:
-
Incident response planning
-
Business continuity integration
-
Disaster recovery strategies
-
Continuous security testing and simulations
-
Post-incident learning and improvement
Organizations are increasingly encouraged by frameworks to develop systems that can withstand, react to, and recover from cyber disruptions in a timely and efficient manner.
How to Implement Cybersecurity Frameworks in Your Organization
1. Assess Current Security Posture
For areas where a cybersecurity framework can enhance policies, controls, and overall risk management approach, start by evaluating current security gaps.
2. Define Roles and Responsibilities
Make sure the Cybersecurity Framework incorporates responsibility and decision-making throughout all security activities by clearly allocating duties to teams and leadership.
3. Develop Policies and Procedures
To direct staff members and stakeholders in uniform, secure practices across the entire company, develop and record rules and procedures that are in line with the Cybersecurity Framework.
4. Conduct Regular Risk Assessments
Assess potential weaknesses, such as exposure to cybersecurity threats, to make sure the Cybersecurity Framework successfully mitigates these risks and maintains system security.
5. Integrate Security into Development
As advised by your Cybersecurity Framework, implement DevSecOps techniques to include security into software development and operations.
6. Implement Continuous Monitoring
Ensure that the Cybersecurity Framework is implemented across networks, cloud environments, and endpoints by deploying monitoring and logging technologies to identify anomalies early.
7. Train Staff Regularly
Incorporate the Cybersecurity Framework into company culture to raise employee understanding of dangers, phishing attempts, and compliance needs.
8. Review and Update Strategies
Make sure the Cybersecurity Framework adapts to new threats and organizational changes by routinely reviewing metrics and audits to improve security rules.
Common Challenges in Adopting Updated Cybersecurity Frameworks
1. Lack of Awareness and Understanding
Employees and management may not completely comprehend the revised Cybersecurity Framework requirements, resulting in inconsistent execution, which causes problems for many firms.
2. Resource Constraints
It is challenging to successfully apply every component of the Cybersecurity Framework due to a lack of funding, personnel, or technological resources.
3. Integration with Existing Systems
The Cybersecurity Framework's implementation may be complicated by the need to coordinate with older IT systems while updating security frameworks.
4. Continuous Monitoring and Maintenance
Ongoing monitoring, upgrades, and audits are necessary to maintain the Cybersecurity Framework, which can be difficult to maintain and resource-intensive.
5. Resistance to Change
The adoption of an updated Cybersecurity Framework may be slowed by teams or employees' resistance to implementing new procedures or security measures.
6. Managing Third-Party Risks
It can be challenging to integrate partners, suppliers, and vendors into the cybersecurity framework, particularly when evaluating and reducing third-party security threats.
As technology continues to evolve, it is increasingly important to stay ahead of cyber risks. A strong cybersecurity framework keeps teams informed and aligned while helping organizations plan for, defend against, and respond to threats. By regularly reviewing and updating security procedures, businesses can reduce risks and enhance their resilience. Implementing a cybersecurity framework thoughtfully and consistently simplifies security management, ensures that everyone understands their roles, and helps the organization maintain confidence in the face of evolving cyber threats.